Internet Security Tools for Personal and Business Use
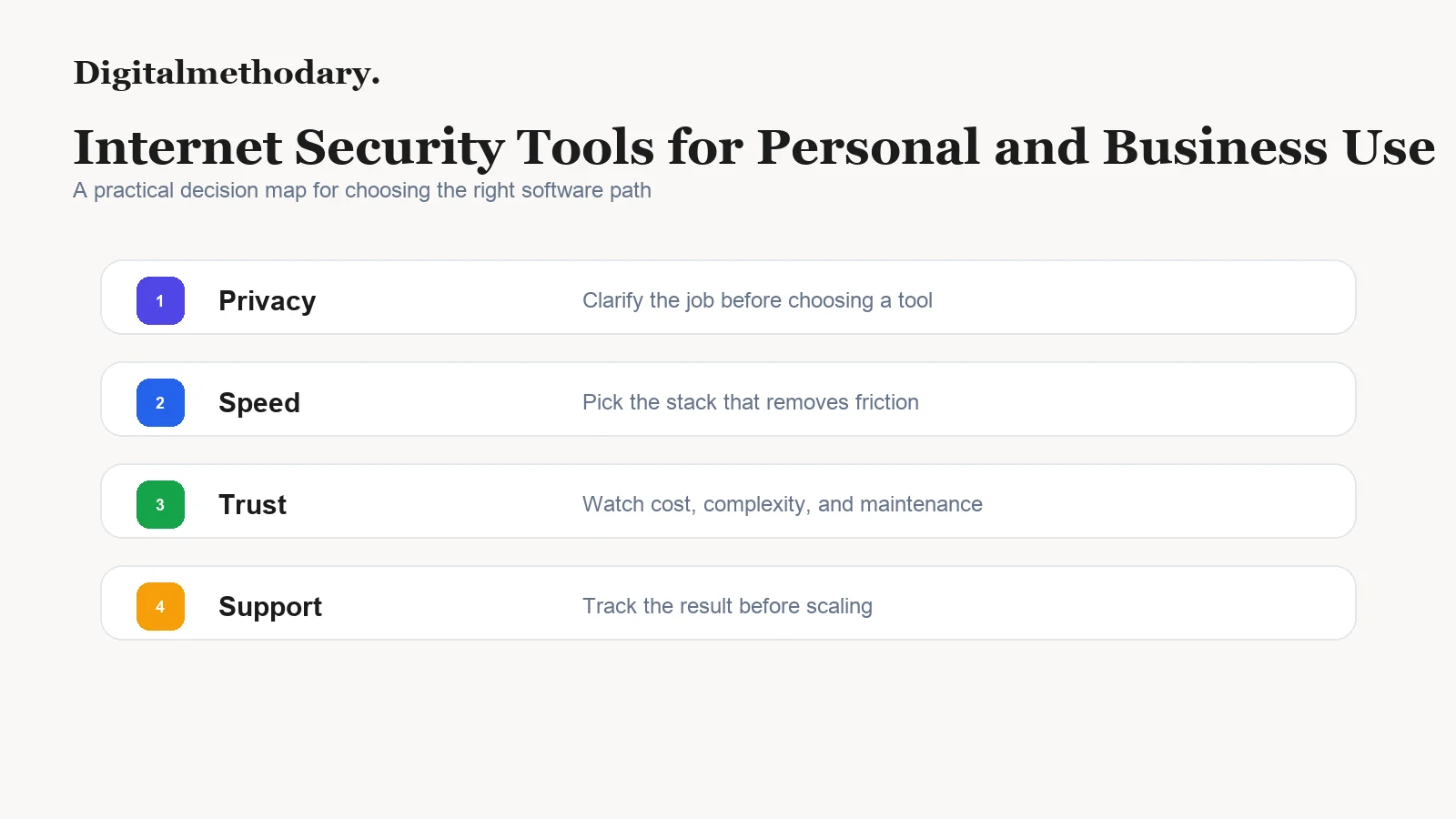
A practical security stack covers four jobs: protect devices, protect accounts, protect networks, and recover quickly when something goes wrong.
Quick Verdict
Strong fit for malware, phishing, and endpoint protection across personal and small business devices.
Best first upgrade when passwords, shared logins, and two-factor recovery are the weak point.
Best for teams that need safer access rules without running a traditional VPN-only setup.
Specific Tool Shortlist
1. Bitdefender
Endpoint and malware protection
Bitdefender is a strong baseline for personal devices and smaller businesses that need malware protection, phishing defense, web protection, and managed security controls.
Where it helps
- Strong reputation for malware and phishing protection.
- Works for both personal plans and business endpoint needs.
- Useful when non-technical users need default protection.
Tradeoffs
- Security suites can include features you may not need.
- Business deployment should be planned, not installed randomly.
Pricing signal: Plan pricing varies by number of devices and business tier.
2. 1Password
Password and secrets hygiene
1Password solves a huge share of everyday security problems: reused passwords, shared credentials, weak recovery processes, and missing two-factor organization.
Where it helps
- Excellent for teams sharing sensitive logins.
- Watchtower alerts expose weak, reused, or breached credentials.
- Strong usability helps adoption.
Tradeoffs
- It only works if the whole team actually uses it.
- Migration requires cleaning up old password habits.
Pricing signal: Personal, family, team, and business tiers are available.
3. Cloudflare Zero Trust
Safer access for teams
Cloudflare Zero Trust is useful when a business needs to control access to internal tools, protect browsing, and reduce reliance on simple shared VPN credentials.
Where it helps
- Access policies can be tied to identity and device posture.
- Useful free and paid entry points for small teams.
- Good fit for remote-first teams using cloud apps.
Tradeoffs
- Configuration decisions matter.
- Not a replacement for password hygiene or endpoint protection.
Pricing signal: Free and paid plans vary by users and security features.
That separation no longer exists.
The same laptop now handles:
- Personal email and banking
- Client files and invoices
- Cloud dashboards and admin access
Which means personal security mistakes become business risks, and small businesses face the same threats as larger companies — just with fewer buffers.
This article introduces a completely different set of internet security tools than earlier guides, chosen specifically to serve both individuals and small businesses without overlap or redundancy.
The Modern Security Reality: Fewer Tools, Better Coverage
Security today is not about piling on software.
It’s about covering distinct failure points:
- Identity access
- Device compromise
- Account takeover
- Email and credential exposure
The tools below are selected so each one protects a different layer, avoiding duplication.
1. Secure Internet Access Without Consumer VPN Hype
Instead of mainstream VPN brands, many privacy-aware professionals and small teams choose infrastructure-driven providers.
Proton VPN — Privacy Infrastructure, Not Marketing
Proton VPN is built by the same team behind encrypted email and privacy services.
Why it’s used by both individuals and businesses:
- Strong jurisdiction and transparency
- Open-source clients
- Clear separation between free and paid tiers
- Designed for privacy-first workflows, not streaming tricks
For small businesses, Proton VPN is often used to:
- Secure remote access
- Protect founders and admins
- Reduce risk on public or shared networks
It’s less flashy — and that’s the point.
2. Password & Access Control That Works for Teams
Many security failures start with shared logins and reused credentials.
Instead of previously mentioned tools, these are commonly adopted by growing teams.
Dashlane — Password Security with Business Visibility
Dashlane is widely used by:
- Consultants
- Agencies
- Small companies scaling beyond “just share the password”
It stands out because it combines:
- Personal password hygiene
- Business-level admin controls
- Breach monitoring and alerts
For individuals, it simplifies secure login.
For businesses, it prevents silent credential sprawl.
Keeper Security — Enterprise-Grade Without Enterprise Complexity
Keeper is popular in regulated and security-conscious environments.
Why small businesses choose it:
- Strong role-based access control
- Audit trails
- Secure sharing without exposing passwords
Keeper is often chosen when account accountability matters more than convenience.
3. Endpoint Security Beyond “Basic Antivirus”
Modern threats are stealthy, not noisy.
That’s why many teams move beyond default protections.
ESET — Lightweight, Serious Endpoint Protection
ESET is trusted by IT professionals because:
- It’s lightweight
- It detects advanced threats
- It works well on older machines
Individuals use ESET for:
- Quiet, always-on protection
Small businesses use it for:
- Consistent protection across all devices
- Centralized control without heavy infrastructure
It’s security that doesn’t get in the way.
Sophos Home — Business-Grade Thinking for Personal Devices
Sophos Home brings enterprise security concepts to home and small business users.
Key advantages:
- Web filtering
- Ransomware protection
- Remote management
This makes it ideal for:
- Families with multiple devices
- Small teams without dedicated IT staff
4. Strong Authentication: Where Most Attacks Actually Fail
Passwords alone are no longer enough.
Authy — Simple Two-Factor Authentication at Scale
Authy is commonly used by:
- Remote workers
- Distributed teams
- Small businesses with many SaaS tools
Why it matters:
- Cloud backup (unlike basic authenticator apps)
- Multi-device access
- Easy recovery
For businesses, this reduces lockout risk while still enforcing strong 2FA.
YubiKey — Physical Security for High-Risk Accounts
YubiKey is used when:
- Admin access matters
- Financial accounts are involved
- Phishing risk must be minimized
Many founders and executives use YubiKey for:
- Cloud admin panels
- Financial services
It’s one of the few tools that phishing cannot bypass.
5. Email Security: The Most Overlooked Attack Surface
Email is still the #1 entry point for breaches.
Proton Mail — Encrypted Email for Sensitive Communication
Proton Mail is widely used by:
- Consultants
- Legal professionals
- Privacy-conscious businesses
It offers:
- End-to-end encryption
- Minimal data retention
- Strong account security
For individuals, it protects personal communication.
For businesses, it reduces exposure of sensitive data.
A Practical Security Stack (Personal + Small Business)
Here’s how these tools fit together without overlap:
- Proton VPN → secure network access
- Dashlane or Keeper → credential control
- ESET or Sophos Home → device protection
- Authy + YubiKey → account security
- Proton Mail → secure communication
Each tool protects a different failure point.
No duplication. No bloat.
Why This Stack Works for Both Markets
Individuals get:
- Strong protection without complexity
- Tools that scale as life gets more digital
Small businesses get:
- Enterprise thinking without enterprise cost
- Security that grows with the team
- Reduced single-point failures
This is what modern internet security tools should do.
Final Thoughts: Security Is No Longer Optional — or Separate
Personal and business internet use are now inseparable.
The smartest approach isn’t buying “business security” or “consumer security” —
it’s choosing tools that work in both worlds.
If your tools can protect you and your work at the same time,
you’re already ahead of most people.
Explore More in Security & VPN Tools
A 12-tool stack with pricing, tax notes, and why we picked each one. One email, no sequence.